Software-Defined Access (SD-Access) represents a fundamental strategy for the advancement of enterprise networks. Through automated policy enforcement, network segmentation, and streamlined operations, organizations are able to construct environments that are both adaptable and secure. However, technology alone is insufficient to ensure robust security; adherence to established best practices is essential throughout the design, implementation, and ongoing management of SD-Access solutions. This article examines cross-vendor recommendations designed to enhance fabric infrastructure in accordance with Zero Trust principles.
Identity‑Driven Access Everywhere
A robust SD‑Access deployment commences with the proper authentication of all devices and users.
- Integration of 802.1X and NAC solutions (such as Cisco ISE, Aruba ClearPass, or Fortinet NAC) with both wired and wireless infrastructures enforces identity‑based access controls.
- Effective device profiling enables differentiated treatment of IoT, BYOD, and corporate assets across multiple vendors.
- To support scalability, organizations should implement role‑based access control (RBAC) or group‑based policies using tags, VLANs, or security groups in place of static ACLs.
Segmentation and Policy Enforcement
Segmentation helps limit the impact of security breaches and supports implementation of least privilege principles.
- Micro-segmentation technologies including Cisco TrustSec/SGTs, VMware NSX distributed firewall, and Aruba Dynamic Segmentation are used to isolate workloads and user groups.
- Policies can be defined in business terms (for example, “Finance apps only interact with Finance users”) rather than relying on IP addresses.
- Inter-group or inter-segment policies should be regularly reviewed to remove broad “allow all” rules.
Infrastructure Hardening and Layer‑2 Protections
Regardless of the vendor, it is essential to ensure that both underlay and overlay fabrics are properly secured.
- Control Plane Protection: Implement Control Plane Policing mechanisms such as CoPP (Cisco), Control Plane Policing (Arista), or equivalent solutions to mitigate traffic floods.
- Management Security: Limit SSH, HTTPS, CLI, and API access exclusively to trusted management networks and integrate Authentication, Authorization, and Accounting (AAA) using TACACS+, RADIUS, or LDAP.
- Patch and Update: Maintain current software and firmware versions by monitoring and applying relevant updates as outlined in vendor advisories, including Cisco PSIRT, Juniper JSA, and Arista security advisories.
- Layer‑2 Security: Activate features such as DHCP Snooping, Dynamic ARP Inspection, and IP Source Guard (or vendor-specific equivalents) to prevent rogue DHCP activity, ARP spoofing, and IP impersonation. These controls are supported on platforms such as Cisco Catalyst/NX‑OS, ArubaOS‑CX, and Juniper EX/QFX series.
- Port Security: Apply broadcast rate limiting, enable BPDU guard, and disable or secure unused ports to enhance overall security posture.
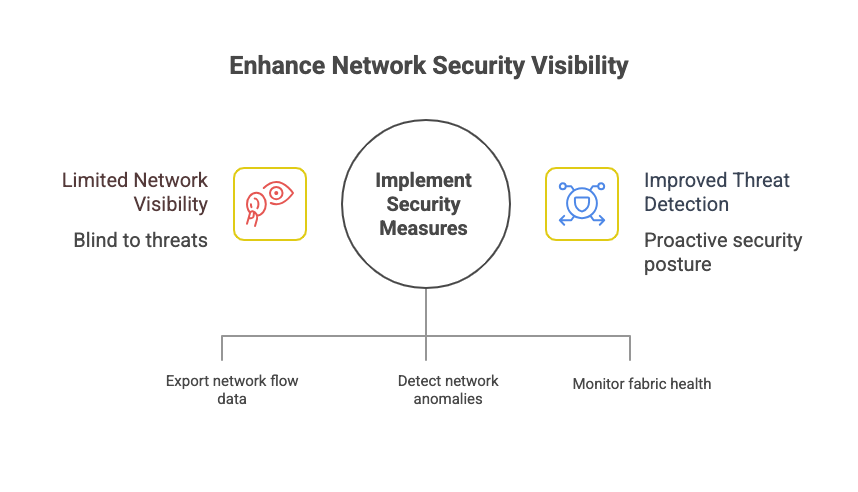
 Visibility and Threat Detection
Visibility and Threat Detection
You cannot protect what you can’t see.
- Telemetry and Flow Monitoring: Export NetFlow, IPFIX, or sFlow from fabric devices for visibility into east‑west traffic.
- Network Detection & Response (NDR): Use tools like Cisco Secure Network Analytics (Stealthwatch), Darktrace, or ExtraHop to detect anomalies.
- Fabric Assurance Platforms: DNA Center, Aruba Central, Juniper Mist, and others provide fabric health dashboards and policy compliance checks.
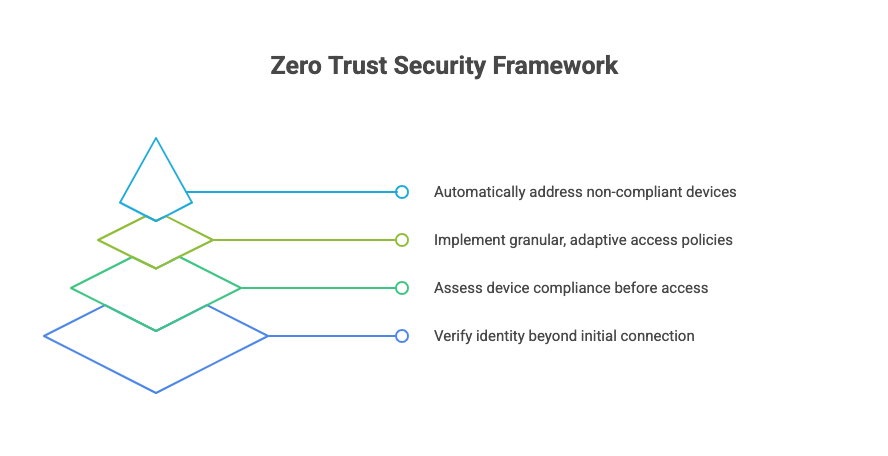
 Embrace Zero Trust Principles
Embrace Zero Trust Principles
Zero Trust is not vendor‑specific—it’s a framework.
- Verify identity continuously, not just at the point of connection.
- Evaluate device posture (OS version, patch level, compliance) before granting full access.
- Enforce least privilege with granular policies that adapt dynamically.
- Automate remediation for non‑compliant devices (quarantine VLANs, restricted policies, or auto‑patching).
 Operational Best Practices
Operational Best Practices
Security is a lifecycle practice.
- Perform regular policy audits and align segmentation with evolving business needs.
- Train network and security teams on interpreting logs and assurance outputs across platforms.
- Establish a rollback strategy before policy changes.
- Document intent and policies in business language for audit and compliance readiness.
 Conclusion
Conclusion
Securing an SD-Access environment involves more than simply enabling basic features. Through the integration of identity-driven access, segmentation, fabric hardening, visibility, and Zero Trust principles, organizations can establish a robust, multi-vendor fabric capable of confronting contemporary security challenges. The recommended best practices presented herein are applicable to infrastructures utilizing platforms such as Cisco, Aruba, Juniper, Arista, or any combination thereof.
Disclaimer: This post is for educational purposes only and does not endorse any specific vendor, architecture or solution.


